ATT&CK is a knowledge base of adversarial techniques. Unlike prior work in this area, the focus is not on the tools and malware adversaries use, but on how they interact with systems during an operation. See What is ATT&CK? for a quick overview.
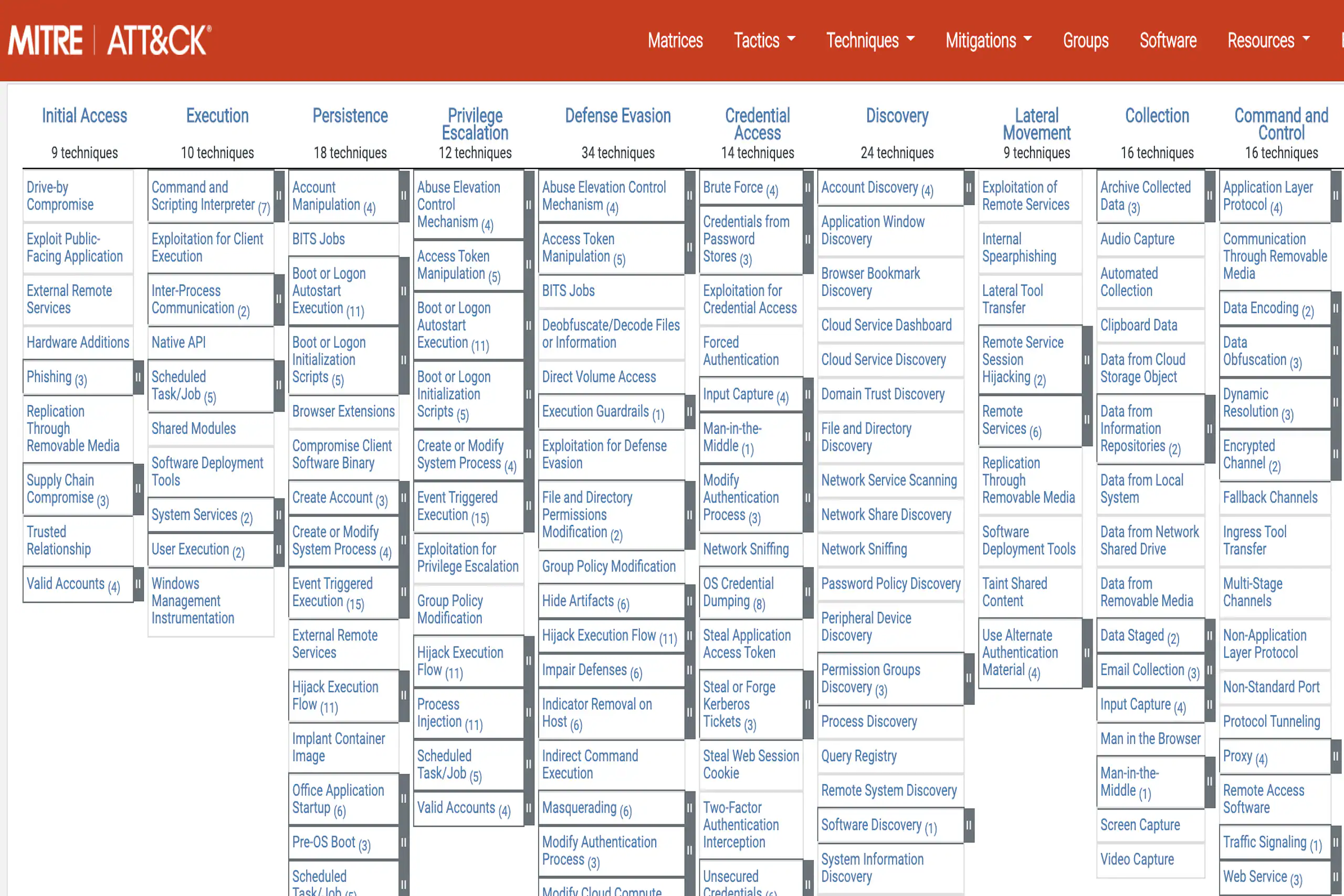
3.1 — The ATT&CK Matrix
The ATT&CK Matrix is a visual representation of the relationship between tactics and techniques.
The Persistence column — an adversary trying to keep their foothold — shows 20 techniques an attacker may use.
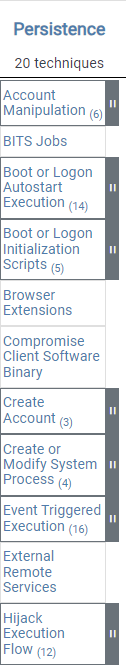
See all Persistence techniques
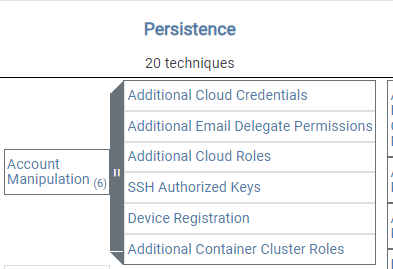
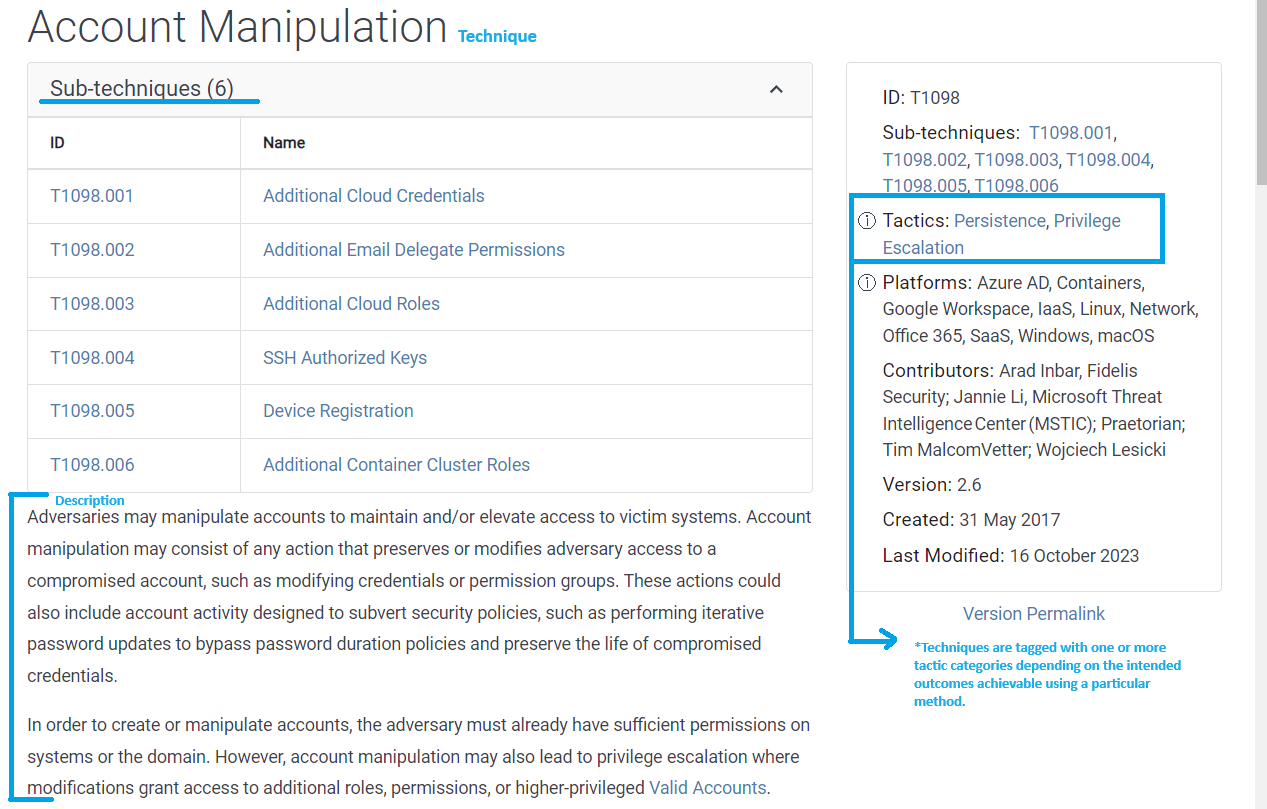
Some techniques break down into sub-techniques. Account Manipulation, for example, has six listed sub-techniques.
Account Manipulation — full details
3.2 — Technology Domains
A technology domain is a specific area or aspect of technology that adversaries interact with or exploit. A platform is the system an adversary is operating within.
MITRE has defined three technology domains, each with associated platforms:
- Enterprise (traditional enterprise networks and cloud technologies) — Linux, macOS, Windows, AWS, Azure, GCP, SaaS, Office 365, Azure AD
- Mobile — Android, iOS
- Industrial Control Systems (ICS)
3.3 — Tactics
Tactics answer the "why" of an attack technique — the adversary's objective for performing an action.
Each technique or sub-technique is associated with one or more tactic categories depending on the intended outcomes. A definition is provided for each tactic, describing the category and serving as a guide for what techniques belong under it.
3.4 — Techniques and Sub-Techniques
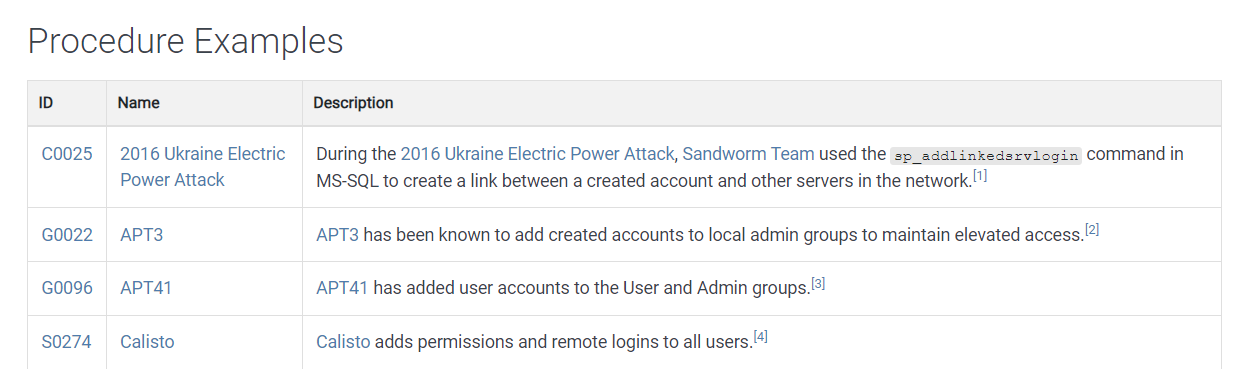
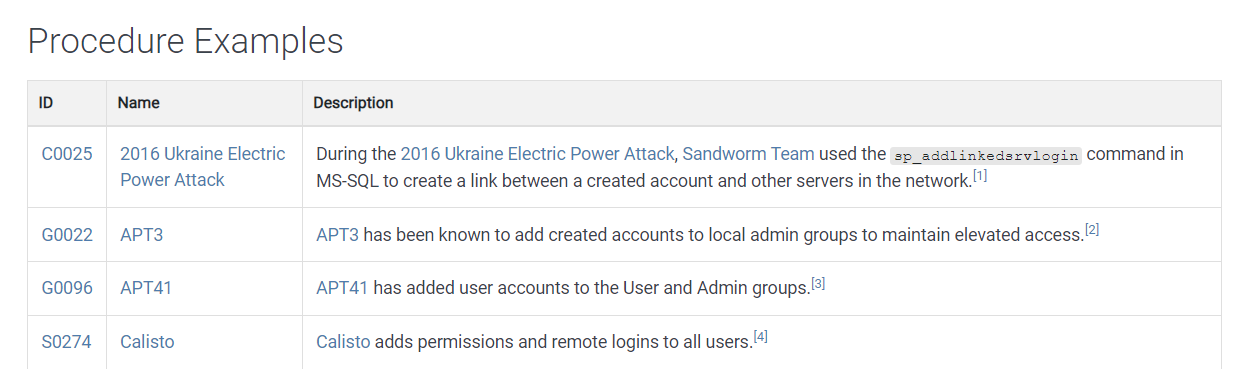
3.4.1 — Procedures
Procedures refer to the step-by-step actions adversaries take using specific techniques or sub-techniques to achieve their goals. For example, APT 13 creates accounts for local administrator groups to maintain elevated access. Procedures can fall under multiple techniques and sub-techniques.
3.4.2 — Technique and Sub-Technique Object Structure
A field explains how a technique or sub-technique works — including descriptions of how adversaries might use it, potential indicators of its use, and other relevant details.
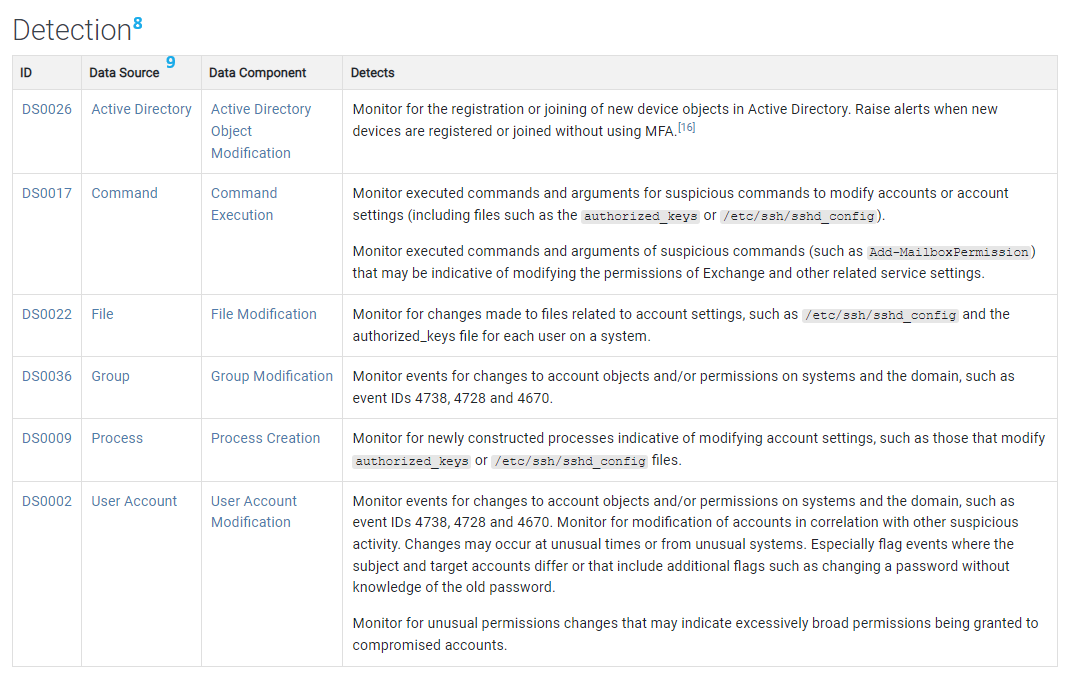
A data source is where data is obtained or collected for processing, analysis, or reporting.
Always Required
- Name
- ID
- Sub-Techniques
- Tactic
- Description
- Platform
- Version
- Detection
- Data Source
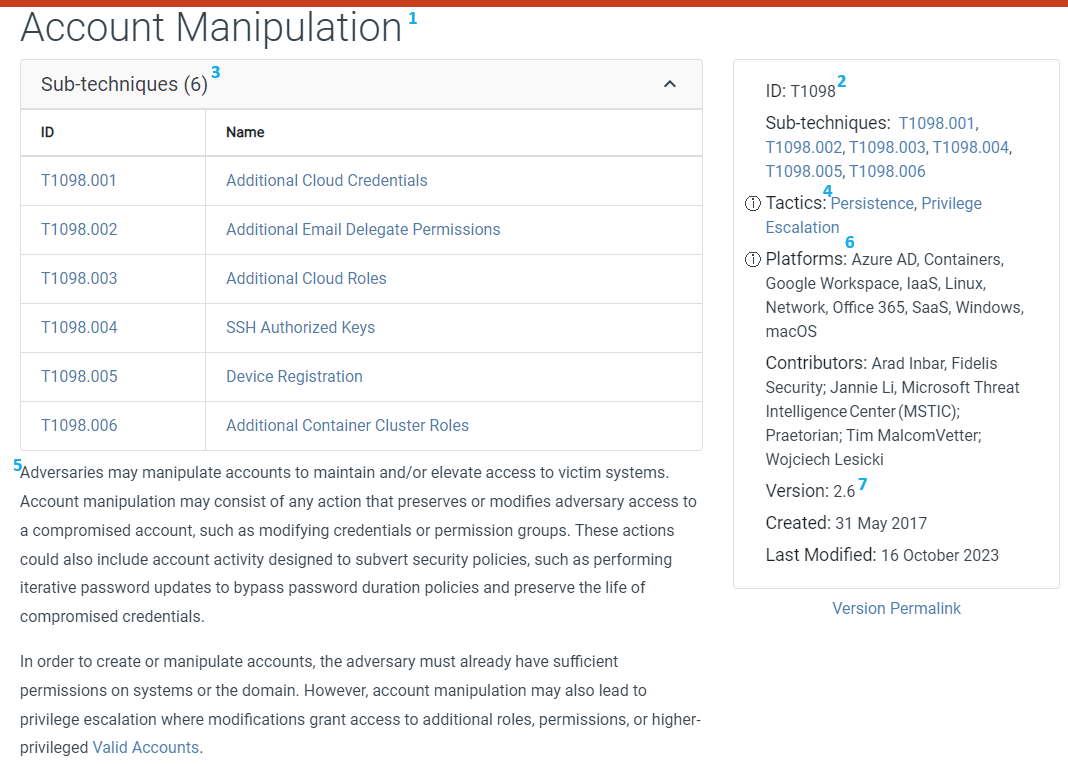
Account Manipulation — full example
Required If Available
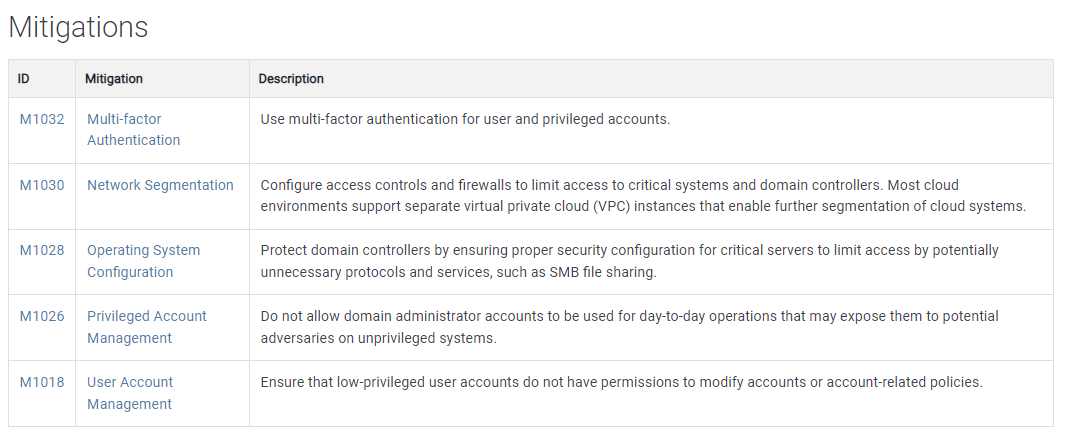
- Mitigation
Required for Sub-Techniques under Privilege Escalation
- Permissions Required
- Effective Permissions
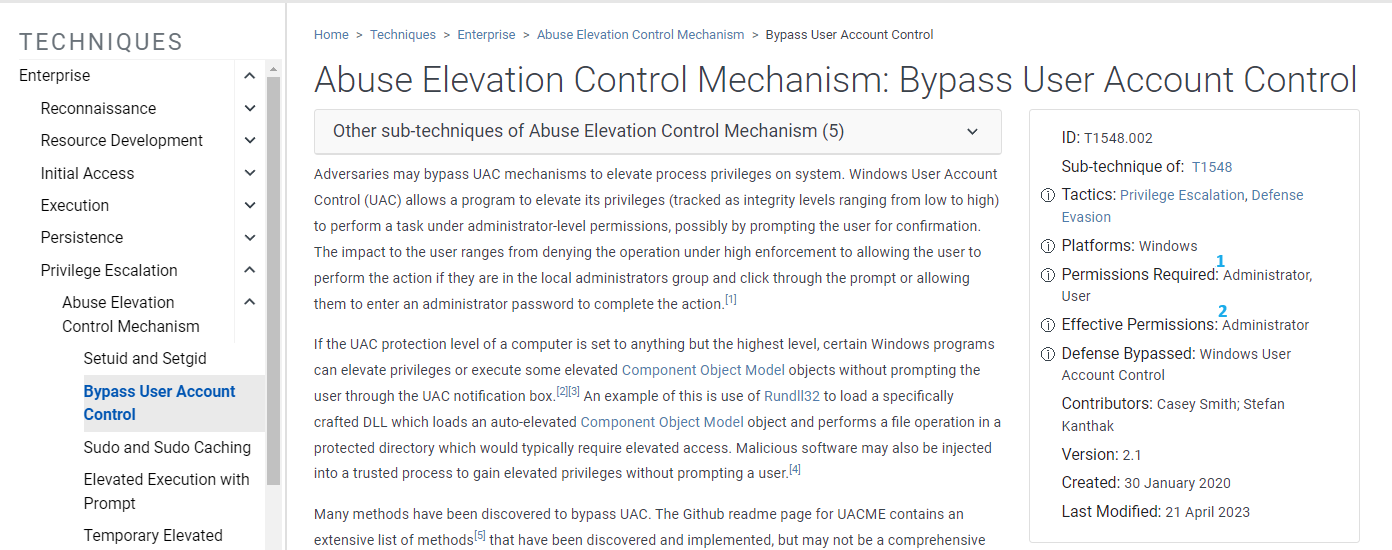
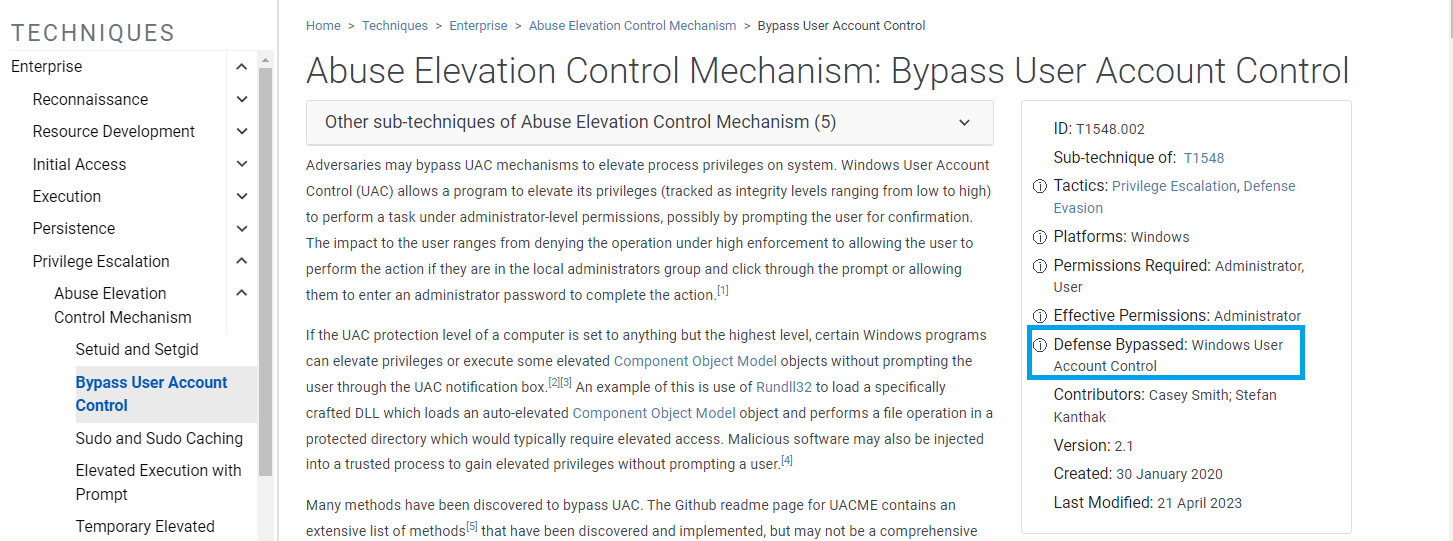
Defense Evasion Requirement
If a technique or sub-technique can be used to bypass or evade a particular defensive tool, methodology, or process, then Defense Bypassed is required to be listed.
Optional
- Link to the CAPEC ID (Common Attack Pattern Enumeration and Classification)
- List of contributors — non-MITRE individuals and organizations that contributed information
- Procedure Example — concrete examples of how specific adversary groups or software have been used in real-world scenarios
Optional — Execution Sub-Technique Fields
- System Requirements — additional information on requirements the adversary needs to meet for an effective attack, such as software and patch level
- Supports Remote — whether the sub-technique enables execution of actions on a system from a remote location
3.4.3 — Sub-Technique Details
Before the addition of sub-techniques in 2020, techniques varied significantly in coverage, making the framework challenging to navigate. MITRE's goals for sub-techniques were to:
- Make the abstraction level of techniques similar across the knowledge base
- Reduce the number of techniques to a manageable level
- Provide a structure to allow sub-techniques to be added easily
- Demonstrate that techniques are not shallow and can have many variations
- Simplify the process for adding new technology domains that use overlapping techniques
- Enable more detailed data sources and descriptions for how a behavior can be observed on specific platforms
Considerations
- While a technique may align with multiple tactics, sub-techniques do not have to apply to all those tactics. For example, a sub-technique under "Process Injection" could also apply to "Defense Evasion" but does not have to apply to any other tactics.
- ATT&CK does not require that every technique have sub-techniques. Example: Multi-Factor Authentication Interception.
- Sub-techniques can be platform-specific, but not all sub-techniques are. Network communications techniques, for example, may not be due to their platform-agnostic nature.
- If information associated with sub-techniques is relevant to the parent technique, it will be rolled up to the parent. For instance, the recommendation to use multi-factor authentication to mitigate against the "Additional Cloud Credentials" sub-technique is equally effective for preventing Account Manipulation efforts more broadly.
The official MITRE ATT&CK Design and Philosophy document references Two-Factor Authentication Interception. This has since been updated to Multi-Factor Authentication Interception to reflect that there are more than two authentication factors: something you are, something you know, something you have, somewhere you are, and something you do.
3.5 — Groups
"Groups are activity clusters that are tracked by a common name in the security community." — MITRE
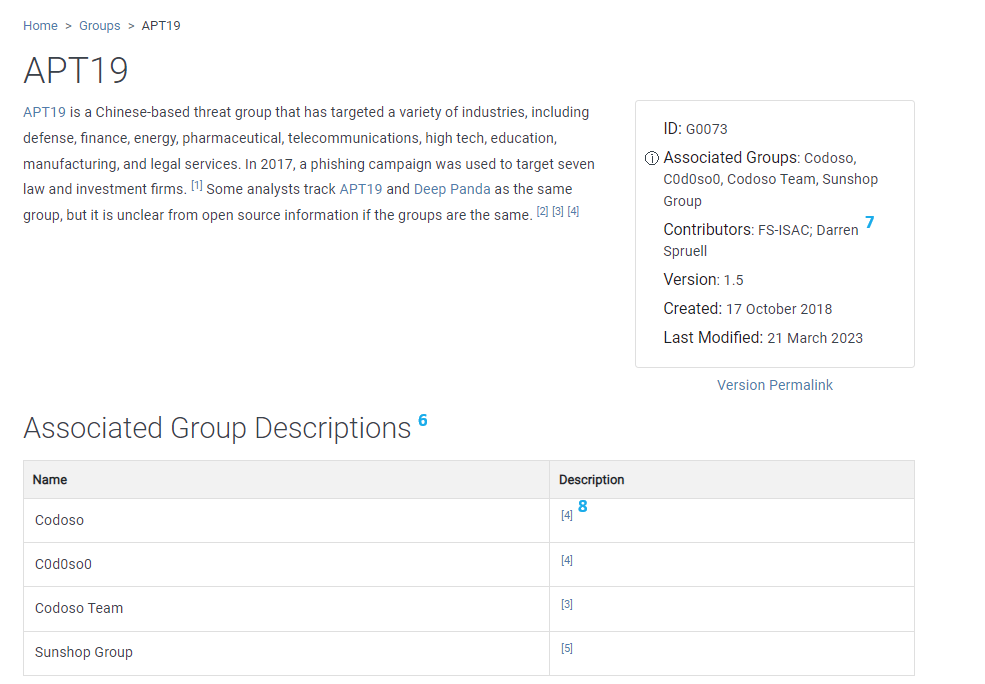
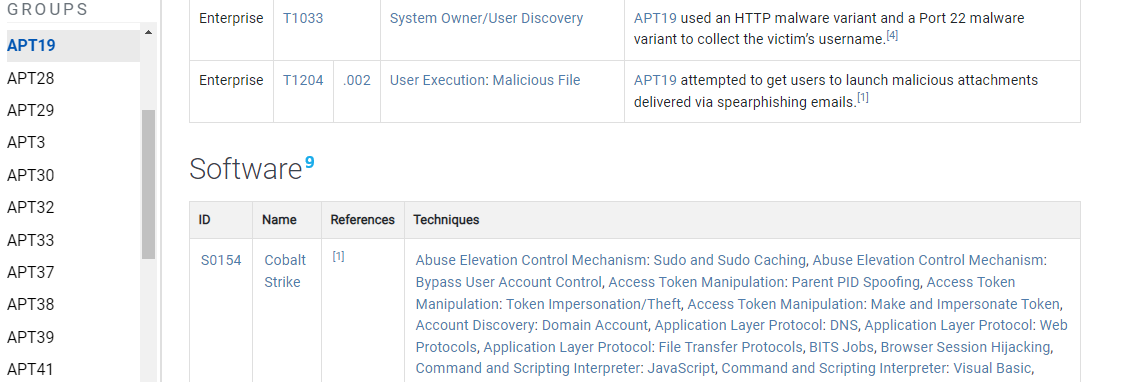
ATT&CK focuses primarily on Advanced Persistent Threat (APT) groups, such as APT 19, but also includes other advanced groups such as FIN10.
3.5.1 — Groups Object Structure
Required
- Name
- ID
- Version
- Description
- Techniques / Sub-Techniques Used
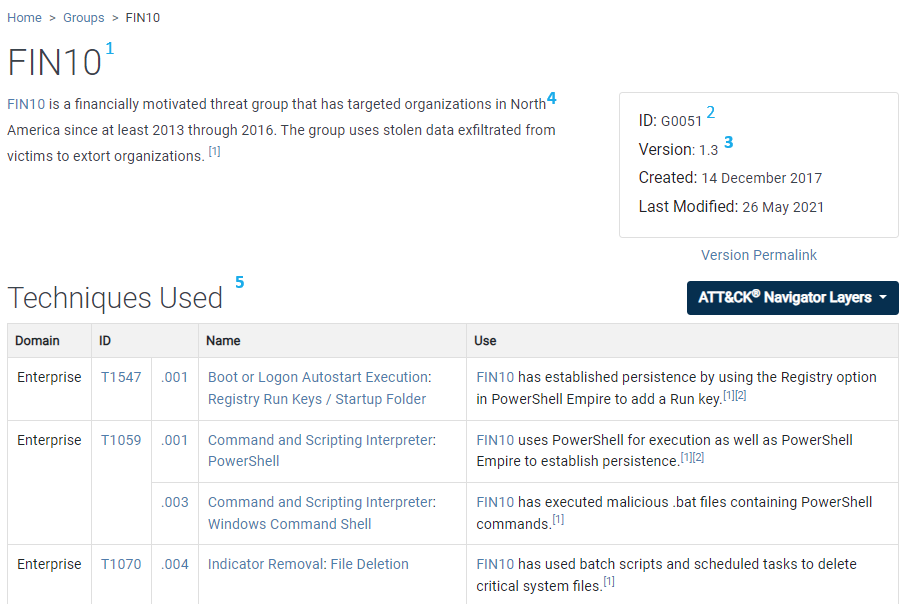
Optional
- Associated Groups
- Contributor
- Associated Group Descriptions
- Software
Coming Soon
- 3.6 — Software
- 3.6.1 — Software Object Structure
- 3.7 — Mitigations
- 3.7.1 — Mitigation Object Structure
- 3.8 — ATT&CK Object Model Relationships
- 3.9 — Versioning (Objects, Techniques, Groups, Software, Matrix, Releases)
The scope of ATT&CK also expands beyond technology domains with PRE-ATT&CK. PRE-ATT&CK covers documentation of adversarial behavior during requirements gathering, reconnaissance, and weaponization before access to a network is obtained.